Security IP
Security IP cores are critical components designed to protect embedded systems from cyber threats by providing encryption, authentication, and secure communication. These cores enhance the security of devices by integrating advanced features like Crypto Accelerator IP, which accelerates cryptographic algorithms, and DPA and FIA Countermeasures IP, which safeguard against side-channel attacks. Inline Memory Encryption IP ensures that sensitive data stored in memory is encrypted in real-time, while Quantum Safe Cryptography IP prepares devices for future-proof security against quantum computing threats. Root of Trust IP establishes a secure foundation for boot processes, and Security Protocol Engine IP manages secure communication protocols for reliable, encrypted data transfer.
-
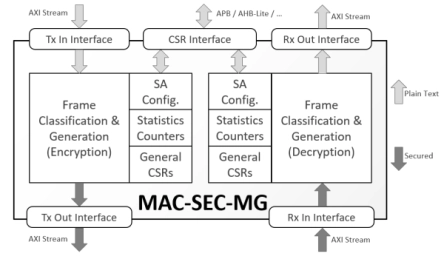
MACsec Protocol Engine for 1G/10G+ Ethernet
- The MAC-SEC-MG IP core implements a compact and configurable custom-hardware protocol engine for the IEEE 802.1AE (MACsec) standard.
- It supports the AES-GCM and AES-GCM-XPN cipher suites provisioned by the MACsec standard and the VLAN-in-Clear improvement.
- The engine is silicon- and performance-optimized for networks operating from 2.5 Gbps to 10 Gbps and beyond; up to 16.75 Gbps is possible with this core.
-
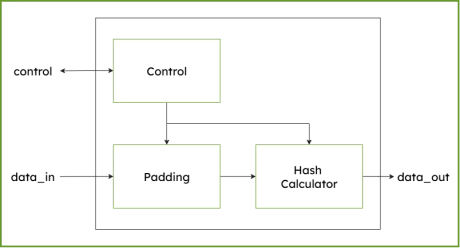
SHA-512/384 - Secure Hash Algorithm IP Core
- Supports SHA-384, SHA-512 and SHA512/256 cryptographic algorithm, an one-way hash function compliant to NIST’s FIPS 180-4 standard.

-
SHA-256 Secure Hash Algorithm IP Core
- Supports SHA-256 cryptographic algorithm, an one-way hash function compliant to NIST’s FIPS 180-4 standard.
-
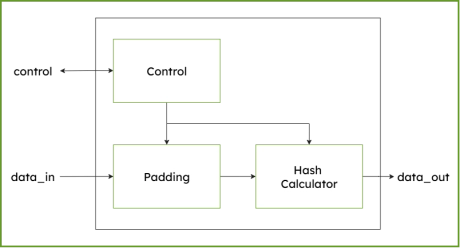
SHA3 Secure Hash Algorithm IP Core (224/256/384/512)
-
Supports SHA-3 hash functions SHA-3-224, SHA-3-256, SHA-3-384, SHA-3-512 and extendable output functions (XOF), SHAKE-128 and SHAKE-256 compliant to NIST´s FIPS 202 standard.
-
-
EdDSA Curve25519 signature generation engine
- The EdDSA Curve25519 extension adds hardware support for modern elliptic-curve cryptography inside DCD-SEMI’s configurable cryptographic co-processor.
- The implementation is based on Curve25519, a widely adopted 255-bit elliptic curve designed for efficient key exchange and digital signatures, with strong resistance to side-channel attacks and high performance in constrained embedded environments.
-
Multi-channel Ultra Ethernet TSS Complete Layer
- The UET-TSS-IP-369 (EIP-369) is an inline, high-performance, multi-channel packet engine that provides the complete TSS layer, bypass/drop and basic crypto processing at rates up to 1.6Tbps.
- The engine is designed for integration into the systems that require TSS processing for one or more ports. The engine is provided as separate ingress and egress data paths.
- The EIP-369 embeds the UET-TSS-IP-69 for the packet transformation.

-
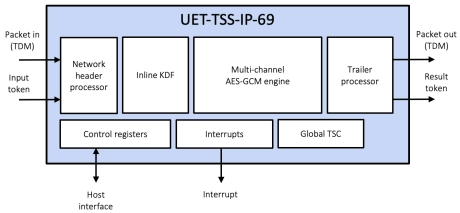
Multi-channel Ultra Ethernet TSS Transform Engine
- The UET-TSS-IP-69 (EIP-69) is a high-performance, multi-channel transform engine that provides the complete TSS packet transformation (including KDF and IP/UDP updates), bypass/drop and basic crypto processing at rates up to 1.6Tbps.
- The engine is designed for integration into the systems that require TSS processing for one or more ports. The engine is provided as separate ingress and egress data paths.
-
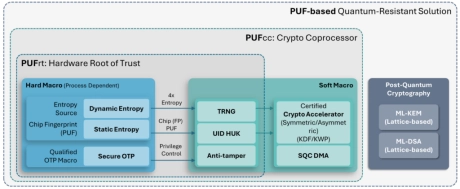
PUF-based Post-Quantum Cryptography (PQC) Solution
- PUFsecurity is proud to pioneer the world’s first PUF-based Post-Quantum Cryptography (PQC) solution, delivering cutting-edge, hardware-level security that sets a new standard.
- Our innovative solution integrates PUF technology with quantum-resistant cryptographic algorithms, ensuring robust key protection and seamless transition to a quantum-secure future.
-
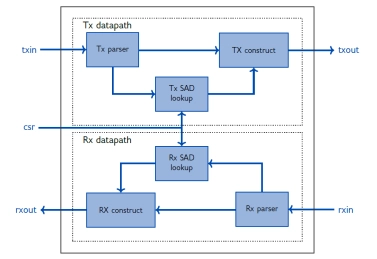
IPSEC AES-256-GCM (Standalone IPsec)
- XIP7213E implements the Internet Protocol Security (IPsec) as standardised in RFC4303 and RFC4305.
- The IPsec protocol defines a security infrastrucure for Layer 3 (as per the OSI model) traffic by assuring that a received packet has been sent by the transmitting station that claimed to send it.
-
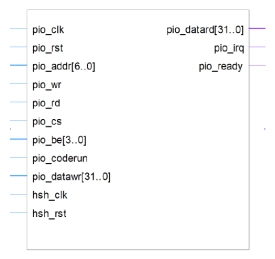
100% Secure Cryptographic System for RSA, Diffie-Hellman and ECC with AMBA AHB, AXI4 and APB
- The DCRP1A - CryptOne IP is a 100% secure cryptographic system
- CryptOne is a fully scalable, hardware-accelerated cryptographic system
- Designed for next-generation SoCs, FPGAs, and secure embedded systems, it delivers 100% secure asymmetric cryptography acceleration for demanding applications.
