Cryptography IP
Welcome to the ultimate Crypto Accelerator IP hub! Explore our vast directory of Crypto Accelerator IP
All offers in
Cryptography IP
Filter
Compare
348
Cryptography IP
from
59
vendors
(1
-
10)
-
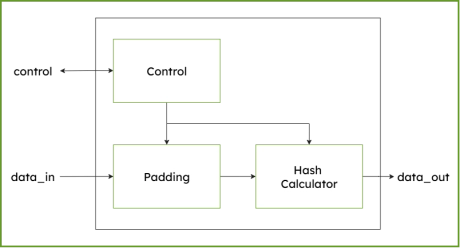
SHA-512/384 - Secure Hash Algorithm IP Core
- Supports SHA-384, SHA-512 and SHA512/256 cryptographic algorithm, an one-way hash function compliant to NIST’s FIPS 180-4 standard.

-
SHA-256 Secure Hash Algorithm IP Core
- Supports SHA-256 cryptographic algorithm, an one-way hash function compliant to NIST’s FIPS 180-4 standard.
-
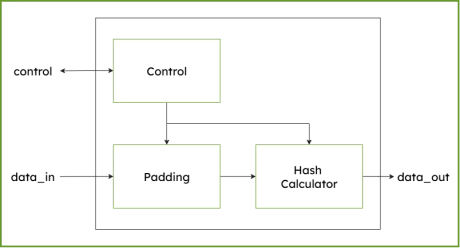
SHA3 Secure Hash Algorithm IP Core (224/256/384/512)
-
Supports SHA-3 hash functions SHA-3-224, SHA-3-256, SHA-3-384, SHA-3-512 and extendable output functions (XOF), SHAKE-128 and SHAKE-256 compliant to NIST´s FIPS 202 standard.
-
-
EdDSA Curve25519 signature generation engine
- The EdDSA Curve25519 extension adds hardware support for modern elliptic-curve cryptography inside DCD-SEMI’s configurable cryptographic co-processor.
- The implementation is based on Curve25519, a widely adopted 255-bit elliptic curve designed for efficient key exchange and digital signatures, with strong resistance to side-channel attacks and high performance in constrained embedded environments.
-
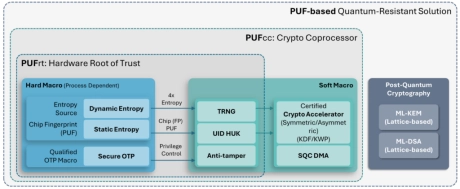
PUF-based Post-Quantum Cryptography (PQC) Solution
- PUFsecurity is proud to pioneer the world’s first PUF-based Post-Quantum Cryptography (PQC) solution, delivering cutting-edge, hardware-level security that sets a new standard.
- Our innovative solution integrates PUF technology with quantum-resistant cryptographic algorithms, ensuring robust key protection and seamless transition to a quantum-secure future.
-
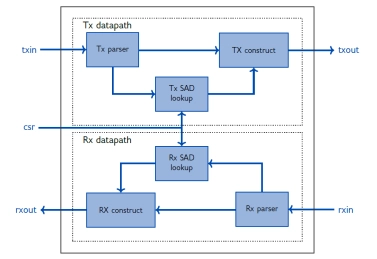
IPSEC AES-256-GCM (Standalone IPsec)
- XIP7213E implements the Internet Protocol Security (IPsec) as standardised in RFC4303 and RFC4305.
- The IPsec protocol defines a security infrastrucure for Layer 3 (as per the OSI model) traffic by assuring that a received packet has been sent by the transmitting station that claimed to send it.
-
100% Secure Cryptographic System for RSA, Diffie-Hellman and ECC with AMBA AHB, AXI4 and APB
- The DCRP1A - CryptOne IP is a 100% secure cryptographic system
- CryptOne is a fully scalable, hardware-accelerated cryptographic system
- Designed for next-generation SoCs, FPGAs, and secure embedded systems, it delivers 100% secure asymmetric cryptography acceleration for demanding applications.

-
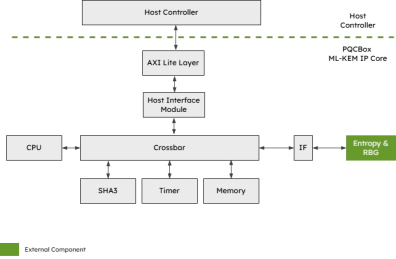
xQlave® ML-KEM (Kyber) Key Encapsulation Mechanism IP core
- Quantum-resistant key exchange for future-proof security
- Compliant with NIST's ML-KEM standard
- Pure RTL without hidden CPU or software components
- Optimised architecture with constant-time execution
-
Highly-optimized PQC implementations, capable of running PQC in under 15kb RAM
- PQCryptoLib-Emebedded is a versatile, CAVP-ready cryptography library designed and optimized for embedded devices.
- With its design focused on ultra-small memory footprint, PQCryptoLib-Embedded solutions have been specically designed for embedded systems, microcontrollers and memory-constrained devices. It provides a PQC integration to devices already in the field.

-
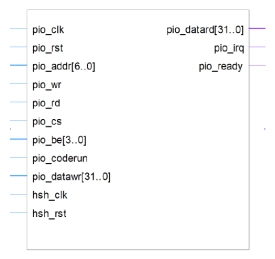
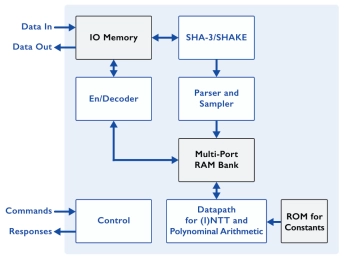
Post-Quantum Key Encapsulation IP Core
- The PQC-KEM is an IP Core for ML-KEM Key Encapsulation that supports key generation, encapsulation, and decapsulation operations for all ML-KEM variants standardized by NIST in FIPS 203.
- ML-KEM is a post-quantum cryptographic (PQC) algorithm, designed to be robust against a quantum computer attack.